In today’s digital world,
protecting your iPhone from hackers is more important than ever.
Our reliance on these devices means a single breach can lead to significant consequences, ranging from stolen personal information to financial losses.
If you suspect your iPhone has fallen prey to a cybercriminal, don’t worry!
In this blog post, we’ll walk you through the telltale signs that your device may have been compromised and share
actionable steps to remove a hacker from my iPhone and secure phone against future threats.
Quick Summary
- Unusual activity or changes in your iPhone’s behavior, mysterious charges, and unauthorized purchases could be signs of a hack.
- To remove a hacker from your iPhone, uninstall suspicious apps and profiles, update to the latest iOS software version, change your Apple ID password, perform a factory reset or seek help from Apple Support.
- Use two-factor authentication for better security and only download trusted apps and install regular security updates to keep your device safe.
Signs Your iPhone Has Been Hacked
Unusual Activity or Behavior on Your Device, such as sudden crashes or unexpected pop-ups appearing.
Unusual Activity Or Behavior On Your Device
One of the first signs that your iPhone may have been hacked is
unusual activity or behavior on your device.
This can manifest in various ways, such as
apps crashing unexpectedly, a
sudden spike in data usage, or even
unexplained battery drain.
Another example of unusual behavior might involve receiving
strange text messages containing random characters or unfamiliar links.
These messages might be attempts to gather your personal information by exploiting
vulnerabilities in your phone’s software.
In such cases, it is crucial to remain vigilant and avoid clicking suspicious links or responding to weird texts.
Mysterious Charges Or Unauthorized Purchases
If you notice
suspicious charges or unauthorized purchases on your iPhone, it could be a sign that a hacker has accessed your device. Reviewing your App Store or iTunes purchase history is one way to check for this.
If you see anything unfamiliar, report it immediately and change your Apple ID password.
To prevent future unauthorized purchases, consider enabling
two-factor authentication for added security. This will require another verification form and entering your password when purchasing your iPhone.
Additionally, only download apps from
trusted sources and avoid clicking on links or downloading attachments from unknown sources, as these can sometimes lead to
phishing scams and other forms of cyberattacks.
Performance Issues And Slow Speeds
If you’ve noticed that your iPhone is suddenly slower and takes longer to perform tasks, it could be a sign that your device has been hacked.
A hacker may have installed
malware or spyware on your phone, which can
slow down its performance by using up resources or redirecting internet traffic.
To remove a hacker from your iPhone, check for
unfamiliar apps or configurations in the Settings menu. Uninstall apps you don’t recognize or trust and promptly delete unknown configurations.
Updating your iOS to the latest version can also help eliminate
vulnerabilities that hackers exploit to gain access to your device.
Unexplained App Appearances And Changes In Settings
If you notice
unfamiliar apps appearing on your iPhone or
settings changing without your knowledge, this could indicate that a hacker has gained access to your device.
For example, you may see
new icons for apps you did not download or recognize on your home screen.
It’s important to address these signs of unauthorized access by uninstalling any unfamiliar apps and configurations as soon as possible. You should also change your Apple ID password immediately to prevent further hacking attempts.
Updating your iOS software version can help fix any security vulnerabilities that hackers may be exploiting.
Tips On How To Remove A Hacker From My iPhone
Here are some practical steps to remove a hacker from your iPhone and keep your device safe, including uninstalling suspicious apps, updating iOS to the latest version, changing your Apple ID password, performing a
factory reset, and seeking help from
Apple Support.
Uninstall Suspicious Apps And Profiles
If you suspect your iPhone has been hacked, one of the first things to do is uninstall any suspicious apps and profiles.
Here are some steps you can follow:
- Go to Settings > General > Profiles & Device Management and delete any suspicious profile you don’t recognize.
- Look through your home screen for any unfamiliar apps. Press and hold an app icon until it jiggles, then tap the X in the corner to delete it.
- Check for apps in the App Library (swipe left from your home screen) and delete any unknown apps.
- If you’re unsure if an app is safe, do a quick online search to see if other users have reported issues.
Removing unauthorized apps and profiles can help prevent further unauthorized access to your iPhone. Remember to change your passwords and update your iOS for added security.
Change Your Apple ID Password
Changing your Apple ID password is critical in removing a hacker from your iPhone. This will prevent the hacker from accessing your personal information or accounts linked to your device.

To change your password, navigate to Settings > Your Name > Password & Security > Change Password. You’ll need to provide security information, such as answers to security questions or authentication through two-factor verification.
I had an experience where my friend’s iPhone was hacked, and she immediately changed her Apple ID password while disconnecting the device from the internet.
All the strange activity stopped once she reconnected her device and signed back into iCloud with the new password.
Update Your IOS To The Latest Version
Updating your iOS to the latest version is essential in removing a hacker from your iPhone. Apple routinely releases software updates that fix security vulnerabilities, bugs, and other issues.
To
update your iOS to the latest version, go to Settings > General > Software Update on your iPhone. If there is a new update available, download and install it immediately.
Keeping up with regular software updates is just one way of maintaining the integrity of your iPhone’s security measures.
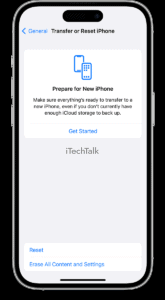
Perform A Factory Reset
Performing a factory reset is one of the most effective ways to remove a hacker from your iPhone. A factory reset will
erase all data and settings, returning your iPhone to its original state.
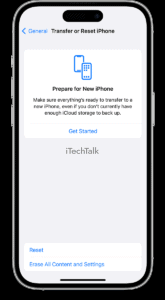
Here are the steps to perform this process:
- Go to Settings on Your iPhone
- Tap General
- Scroll down and tap on Reset
- Select Erase All Content and Settings
- Enter your passcode if prompted
- Confirm your decision by tapping Erase iPhone.
Note: Back up any important data before performing a factory reset, as all data and settings will be erased permanently.
By following these steps, you can successfully remove a hacker from your iPhone and keep it safe and secure in the future.
Remember, taking proactive measures like regularly updating software, using strong passwords, and avoiding suspicious downloads or links can also help prevent hackers from accessing your device in the first place.
Seek Help From Apple Support
If you suspect your iPhone has been hacked, seeking help from Apple Support can be a
reliable option.
The support team can guide you through checking for hacks and removing them from your device.
Apple Support is available 24/7, online or over the phone, to assist with any concerns about iPhone security. Their experts are knowledgeable in
iOS security measures and
data privacy protection.
They can advise on password management, network security, two-factor authentication, digital identity protection, phishing prevention, and
malware removal.
If necessary, they can also access tools to troubleshoot or remotely remove suspicious activity from your iPhone.
Precautions For Future Protection From Hacking
To prevent future hacks, use two-factor authentication and regularly update your security measures.
Use Two-Factor Authentication For Better Security
I highly recommend using two-factor authentication for better security on your iPhone.
With this feature, you will be
prompted to enter a code in addition to your password each time you log in to an app or service, making it much
more difficult for hackers to gain access.
Go to Settings > Your Name > Password & Security > Two-Factor Authentication to enable two-factor authentication. From there, follow the prompts and
register a trusted device to receive verification codes.
This could be another Apple device or phone number associated with your account.
Install Regular Security Updates And Only Download Trusted Apps
Keeping your iPhone safe and secure includes installing
regular security updates and only downloading apps from
trusted sources.
Here are some tips to follow:
- Always update your iOS software to the latest version available. This will help fix any known vulnerabilities in the system that could be exploited by hackers.
- Don’t jailbreak your iPhone, which can compromise its security and make it vulnerable to attacks.
- Only download apps from the App Store or reputable developers. Be cautious of third-party app stores or websites offering free downloads, as these may contain malware or viruses.
- If an app requests access to your personal information or device settings that don’t seem necessary for its functionality, don’t permit it.
- Review app permissions regularly and revoke access if you no longer use the app or if it’s suspicious.
- Stay away from phishing emails or texts that ask you to click on a link or download an attachment. These often lead to fake login pages designed to steal your passwords.
- Use two-factor authentication whenever possible, especially for sensitive accounts like your Apple ID. This adds an extra layer of security by requiring a unique code sent to your phone each time you log in.
By following these tips, you can reduce the risk of having a hacker invade your iPhone and protect yourself against cyber threats.
Avoid Public Wi-Fi And Clicking On Suspicious Links Or Downloads
I always make sure to
avoid public Wi-Fi when using my iPhone. Hackers can easily
intercept data sent over unsecured networks, potentially gaining access to personal information such as passwords and credit card details.
Another important aspect of protecting your iPhone is avoiding clicking suspicious links or downloads.
Scammers often use
phishing tactics to trick users into downloading malware onto their devices or entering sensitive information into fake websites.
Taking these precautions and staying vigilant against potential security threats can help keep your iPhone safe from hackers and other
cybercriminals.
Use VPN To Encrypt Your Internet Connection
Another way to
protect your iPhone from hackers is by
using a VPN, or virtual private network.
A VPN
encrypts your internet connection and
hides your IP address, making it difficult for hackers to track and access your online activity.
With a VPN, you can browse the internet safely and securely without worrying about eavesdropping or surveillance. Many
reputable VPN providers offer easy-to-use mobile apps that allow you to connect quickly and easily.
Using a VPN protects your iPhone from potential hacks and provides an
additional privacy shield for your data online.
Conclusion And Final Thoughts On Keeping Your iPhone Safe And Secure
To remove a hacker from your iPhone, it’s important to be vigilant and take immediate action when you notice any unusual activity.
Uninstalling suspicious apps,
changing passwords,
updating software, and performing a factory reset are effective ways to eliminate hackers’ presence from your device.
However, prevention is key to maintaining iPhone security. Always use strong passwords, enable two-factor authentication, avoid public Wi-Fi networks, and be cautious when downloading apps or clicking links.
 To change your password, navigate to Settings > Your Name > Password & Security > Change Password. You’ll need to provide security information, such as answers to security questions or authentication through two-factor verification.
I had an experience where my friend’s iPhone was hacked, and she immediately changed her Apple ID password while disconnecting the device from the internet.
All the strange activity stopped once she reconnected her device and signed back into iCloud with the new password.
To change your password, navigate to Settings > Your Name > Password & Security > Change Password. You’ll need to provide security information, such as answers to security questions or authentication through two-factor verification.
I had an experience where my friend’s iPhone was hacked, and she immediately changed her Apple ID password while disconnecting the device from the internet.
All the strange activity stopped once she reconnected her device and signed back into iCloud with the new password.
 Here are the steps to perform this process:
Here are the steps to perform this process: